Two-thirds of the largest healthcare data breaches in U.S. history originated from third-party vendors rather than hospitals, according to federal records and independent breach analyses.
These vendor-related incidents have collectively exposed hundreds of millions of patient records, including the 192.7 million-record breach at Change Healthcare in 2024 — the largest ever recorded.
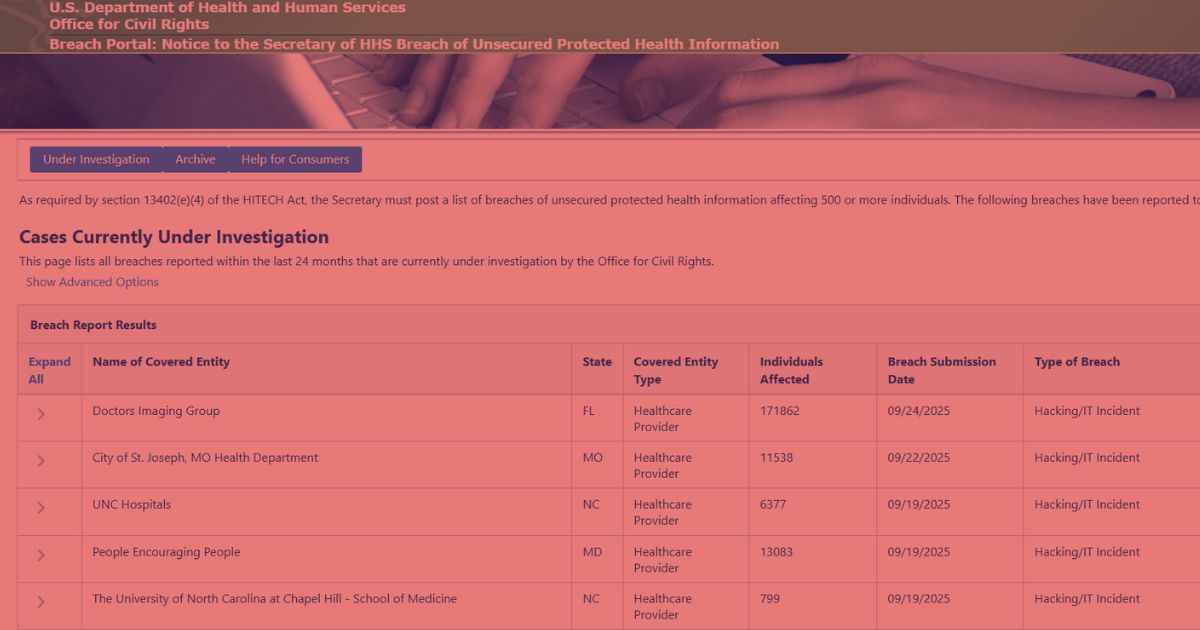
The HIPAA Journal’s September 2025 report shows an apparent slowdown in new breach disclosures. Only 26 incidents affecting 1.29 million individuals were logged on the U.S. Department of Health and Human Services’ Office for Civil Rights (OCR) portal.
However, this decline does not indicate a genuine drop in breaches. Due to the federal government shutdown, OCR stopped updating its public portal on September 24, delaying multiple pending reports.
September 2025: Lowest Monthly Breach Count Since 2018
As of late October, OCR’s database lists 26 large incidents, a 56% decrease from August’s 64. The largest were network-server attacks at Goshen Medical Center (456,385 affected) and Medical Associates of Brevard (246,711 affected). Only one event, involving La Perouse LLC in Nevada, was attributed to a business associate.
Even with incomplete data, the year-to-date total stands at 469 large healthcare breaches, compared with 554 during the same period in 2024. This signals a temporary reporting lag rather than improved security posture.
Historical Data: Vendors Behind Two-Thirds of Major Breaches
While September’s sample leans toward healthcare providers, long-term data reveals that vendors are responsible for most large-scale breaches. Of the 20 largest healthcare breaches on record, 13 originated from vendors such as business associates, billing processors, and analytics firms.
Notable cases include Welltok, PJ&A, Maximus, and HealthEC, all compromised through MOVEit file-transfer exploits in 2023. The 2024 Change Healthcare ransomware attack, which exposed nearly 200 million patient records, further illustrates the systemic risk of vendor dependencies.
A single compromised vendor can disrupt claims processing across multiple hospitals and insurers and trigger multi-client, nationwide exposure within days.
Largest U.S. Healthcare Data Breaches of All Time
| Year | Entity | State | Entity Type | Individuals Affected |
|---|---|---|---|---|
| 2024 | Change Healthcare, Inc. | MN | Business Associate | 192,700,000 |
| 2015 | Anthem Inc. | IN | Health Plan | 78,800,000 |
| 2023 | Welltok, Inc. | CO | Business Associate | 14,782,887 |
| 2024 | Kaiser Foundation Health Plan, Inc. | CA | Health Plan | 13,400,000 |
| 2019 | Optum360, LLC | MN | Business Associate | 11,500,000 |
| 2023 | HCA Healthcare | TN | Business Associate | 11,270,000 |
| 2015 | Premera Blue Cross | WA | Health Plan | 11,000,000 |
| 2019 | Laboratory Corp. of America (LabCorp) | NC | Provider | 10,251,784 |
| 2015 | Excellus Health Plan, Inc. | NY | Health Plan | 9,358,891 |
| 2023 | PJ&A (Perry Johnson & Associates) | NV | Business Associate | 9,302,588 |
| 2023 | Maximus, Inc. | VA | Business Associate | 9,179,390 |
| 2023 | Managed Care of North America | GA | Business Associate | 8,627,242 |
| 2014 | Community Health Systems | TN | Provider | 6,121,158 |
| 2023 | PharMerica Corporation | KY | Provider | 5,815,591 |
| 2025 | Yale New Haven Health System | CT | Provider | 5,556,702 |
| 2024 | Ascension Health | MO | Provider | 5,466,931 |
| 2025 | Episource, LLC | CA | Business Associate | 5,418,866 |
| 2011 | SAIC | VA | Business Associate | 4,900,000 |
| 2023 | HealthEC LLC | NJ | Business Associate | 4,786,241 |
| 2025 | Blue Shield of California | CA | Business Associate | 4,700,000 |
Source: U.S. HHS OCR Breach Portal, compiled by HIPAA Journal and independent HostScore analysis.
Why Vendors Remain the Weak Link?
Business associates, including billing processors, data-hosting providers, and analytics vendors, remain the most vulnerable tier in the healthcare data ecosystem. They typically operate outside the direct oversight of the hospitals and health plans they serve, which weakens compliance enforcement and incident visibility.
Common risk factors include shared cloud infrastructures, misconfigured servers, delayed software patching, and limited monitoring of subcontractor networks. Each creates an entry point that attackers can exploit at scale.
According to the Identity Theft Resource Center (ITRC), third-party and supply-chain compromises rank among the top three breach causes across all U.S. industries. Ransomware operators increasingly favor vendor ecosystems, as a single intrusion can cascade through multiple healthcare clients, exposing millions of patient records in one coordinated strike.
HIPAA-Compliant Hosting as a First Line of Defense
The surge in vendor-driven breaches confirms that security must begin at the hosting layer, not at the application level. When healthcare vendors deploy workloads on shared or poorly segmented cloud environments, a single misconfiguration or weak credential can expose vast amounts of protected health information (PHI). A compliance-aligned hosting foundation protects sensitive data before any application or user interaction occurs.
For example, Atlantic.Net’s HIPAA-Compliant Hosting illustrates how secure infrastructure can reduce breach exposure and simplify compliance for healthcare vendors. The platform is SOC 2 and SOC 3 certified, HIPAA and HITECH audited, and purpose-built to safeguard electronic protected health information (ePHI).
Its architecture combines:
- Dedicated firewalls that block unauthorized access and external threats.
- Encrypted data storage and transmission to prevent interception or tampering.
- Isolated compute environments that contain workloads and restrict lateral movement.
- Continuous monitoring that detects anomalies in real time.
By embedding these security and compliance controls at the infrastructure level, HIPAA-compliant hosting enables healthcare vendors to meet federal privacy mandates without relying solely on software defenses. Yet HostScore’s platform analyses reveal that most vendors still operate on generic cloud stacks lacking verified certifications, encryption attestation, or documented audit trails.
In an interconnected healthcare ecosystem, the hosting environment has effectively become the new security perimeter. Platforms engineered for HIPAA compliance remain one of the most effective first lines of defense against large-scale data breaches.
Key Takeaway
The apparent decline in 2025 breach figures reflects delayed federal reporting rather than improved security. Over ten years of records confirm that two-thirds of major healthcare data breaches originated from third-party vendors.
As healthcare networks become increasingly interconnected, vendor infrastructure and compliance verification have become essential. True data protection begins at the hosting layer, where audited and HIPAA-aligned providers establish measurable standards for safeguarding patient information and maintaining regulatory compliance.
Sources:
- HIPAA Journal – September 2025 Healthcare Data Breach Report (October 22, 2025)
- U.S. Department of Health and Human Services (HHS) – Office for Civil Rights Breach Portal
- Identity Theft Resource Center (ITRC) 2025 Q3 Data Breach Report
- HostScore independent data analysis, October 2025
