Web hosting forms the backbone of your online presence — but it can also become your biggest security risk.
While many site owners invest in plugins, firewalls, and CDN protection, they often overlook vulnerabilities built into their hosting environment. This includes weaknesses in shared hosting, VPS isolation gaps, outdated server software, or poor access controls.
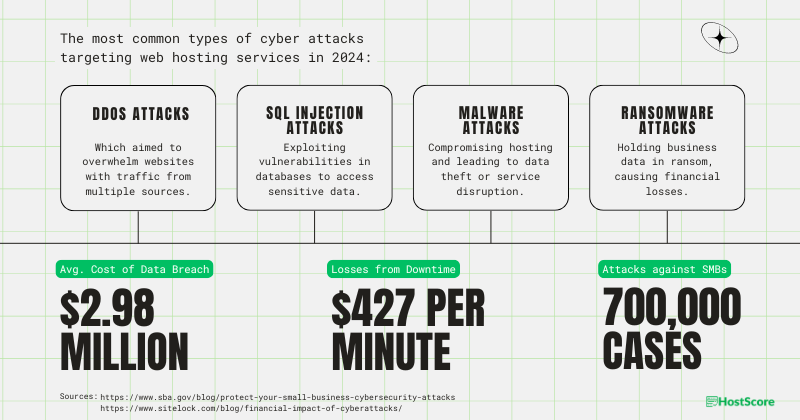
Whether you’re using a budget host or a cloud-based platform, your website may be exposed to threats like DDoS attacks, malware injections, insecure configurations, and more.
In this article, we’ll explain 14 common web hosting vulnerabilities, how they affect your website, and what you can do to stay protected.
Generate Unlimited Free SSLs from One Place
Managing multiple SSLs on different platforms can be frustrating. ZeroSSL.com lets you generate and manage unlimited SSL certificates for just $10 per month – Secure your sites in just 5 minutes.
1. Botnet-Building Attempts
Malicious actors have been known to target entire web servers in their attempts to build Botnets. In these attempts, common targets include web server frameworks and generally involve publicly available exploits.
These advanced and concentrated efforts can often overcome less resilient web hosting providers. Thankfully, once discovered, the vulnerabilities are typically patched fairly rapidly by most web hosts.
2. DDoS Attacks

Distributed Denial of Service (DDoS) isn’t a vulnerability, but as the name implies, is a form of attack. Malicious actors attempt to flood a server (or particular service) with an overwhelming amount of data.
Web hosting services which are not prepared for this can be paralyzed by these attacks. As more resources are consumed, websites on the server are left unable to respond to real queries from visitors.
3. Web Server Misconfigurations
Basic website owners, especially those on cheap shared hosting, will often have no idea whether their servers have been configured properly or not. A significant number of issues can arise from poorly configured servers.
For example, the running of unpatched or outdated applications. Although there are error handling mechanisms for technical issues that arise during execution, flaws can remain unseen until exploited.
Inaccurate configuration in the server, can cause the server to not verify access rights correctly. Hiding restricted functions or links to the URL alone is insufficient as hackers can guess the probable parameters, typical locations and then do a brute-force access.
As an example of this, an attacker can make use of something as small and simple as an unprotected JPEG to gain admin access to the server. They modify a simple parameter that points to an object in the system and then they are in.
4. Lack of Isolation in Shared Hosting Environments
Shared hosting environments do not truly isolate websites.
Although each account has its own directory and resource allocation, all sites reside on the same physical server. This means that the underlying file system, memory, and processor are shared across hundreds of users.
If one account is compromised — say, through a weak password or outdated plugin — an attacker might gain lateral access to other sites on the same server. Even if files aren’t directly exposed, resource-hogging malware or DDoS attacks on one site can slow down or crash others.
Bottom line: If your host doesn’t implement strict containerization or account-level resource controls, your site’s fate is tied to your neighbors’.
5. Unpatched Software and Known Vulnerabilities
Unpatched software is one of the most exploited hosting vulnerabilities.
This applies to operating systems, control panels (like cPanel or Plesk), mail servers, and even installed CMSs. On shared servers, where each account may run different scripts or applications, the risk multiplies.
Web hosts that don’t regularly update server-level software or monitor for CVEs (Common Vulnerabilities and Exposures) leave the door open to known exploits. In some cases, even a single outdated library or plugin can compromise the entire server.
A responsible host should patch vulnerabilities quickly and use tools like vulnerability scanners to monitor threats continuously.
6. Malware Injection and File System Exploits

In a similar fashion to software vulnerabilities, Malware can have a profound impact on a shared hosting server. These malicious programs can find their way onto shared hosting accounts in so many ways.
There are so many types of viruses, trojans, worms, and spyware that anything is possible. Because of the nature of shared hosting, if your neighbor has it – you will likely catch it as well, eventually.
7. Risks of Shared IP Addresses in Hosting
In most shared hosting setups, all websites on the server use the same public IP. If one site sends spam, hosts malware, or engages in abusive behavior, that IP address can get flagged or blacklisted.
This affects everyone on the same IP. Your emails may go to spam, search engines might throttle your visibility, or security services may block access altogether. Worse, requesting IP delisting is tedious and not always successful.
Dedicated IPs can reduce this risk, but not all shared hosting providers offer them or charge extra when they do.
8. Cross-Site Request Forgery (CSRF) Attacks
Also known as cross-site request forgery (CSRF), this flaw is typically observed affecting websites based on poorly secured infrastructure. At times, users save their credentials on certain platforms and this can be risky if the corresponding website does not have a strong infrastructure.
This is especially common on web hosting accounts which are accessed regularly. In these scenarios, the access is repetitive so credentials are usually saved. Through forgery, users are encouraged to perform an action that they didn’t plan in the first place.
These techniques have in recent times outlined potential weakness to account takeovers in various popular hosting platforms including Bluehost, Dreamhost, and HostGator.
Consider this:
An example of this can be demonstrated as a typical financial fraud scenario.
Attackers can target CSRF-vulnerable persons visiting a valid URL. An automatically executed masked code snippet on the site can instruct the target’s bank to transfer funds automatically.
The code snippet can be buried behind an image perhaps, using codes such as the following:
<img src=http://example.com/app/transferFunds?amount=1500&destinationAccount=4673243243 width=0 height=0 />
*Note: This is merely an example and the code will not work.
9. SQL Injections
For any website or online platform, the most important constituent is data. It is used for projections, analysis and various other purposes. Secondly, if confidential financial information like credit card pins gets into the wrong hands, it can create massive problems.
Data sent to and from a database server must pass through reliable infrastructure. Hackers will try to send SQL scripts to servers so they can extract data such as customer information. This means you need to scan all queries before they reach the server.
If a secure filtering system is not in place, important customer data can be lost. IT should be noted though that such an implementation will increase the time taken to extract records.
10. Cross-Site Scripting (XSS) Exploits
XSS attacks inject malicious scripts into your website’s frontend.
Most often using JavaScript, attackers embed code into comment boxes, search fields, or other user-input areas. When a visitor loads the page, the script executes in their browser, potentially stealing session cookies, login tokens, or form data.
Some XSS payloads redirect users to phishing sites or display fake login forms. Others quietly track user activity or modify website content without your knowledge.
Even if your host isn’t directly responsible for the vulnerability, weak server-side input filtering and outdated CMS versions can make your site more susceptible.
11. Weak Encryption & Insecure Cryptographic Protocols
Some hosts still support outdated SSL/TLS versions or use poor randomness sources.
Modern encryption relies on strong algorithms and secure random number generation. On some hosting servers (especially those without recent OpenSSL updates), entropy is low, increasing the chance of predictable encryption keys.
This weakens HTTPS security, putting login credentials, payment details, and personal data at risk. Attackers can exploit these weaknesses to decrypt intercepted data or impersonate legitimate users.
A secure host should enforce strong TLS versions (1.2 or higher), disable deprecated ciphers, and use updated libraries for SSL generation.
12. Virtual Machine Escape in VPS and Cloud Environments
Virtual Machine (VM) escape is a rare but severe threat to VPS and cloud environments.
In a virtualized setup, multiple VMs run on the same physical hardware via a hypervisor. If the hypervisor has a vulnerability, an attacker could break out of their VM and access others.
Although most major cloud providers patch these issues quickly, cheap VPS hosts may lag in security updates. VM escape flaws like VENOM or L1TF have proven that isolation at the hypervisor level is not foolproof.
Choose a provider that actively monitors for such threats and keeps their virtualization stack updated.
13. Third-Party Software and Supply Chain Risks
While resource distribution is a major advantage of cloud hosting, it can also be a point of weakness.
If you’ve heard the term “you are only as strong as your weakest link”, that applies perfectly to the Cloud.
Sophisticated attack and rests mainly on the cloud service providers. This is not specific to the cloud and can happen anywhere else. Downloads from live update servers can be added with malicious functionality. So, imagine the many users who have downloaded this software. Their devices will be infected with this malicious program.
14. Exposed and Poorly Secured APIs
APIs allow developers to manage servers, automate tasks, and integrate services. However, if these interfaces lack proper authentication, rate-limiting, or encryption, they become easy targets.
Many cloud hosts offer API-based controls for DNS records, virtual machine provisioning, and storage access. If these endpoints are misconfigured or publicly exposed, attackers can exploit them using brute-force attempts or token manipulation with minimal technical skill.
Because APIs are often reused across apps and services, a single vulnerability can have ripple effects throughout your hosting environment.
How to Check If Your Hosting Provider Protects Against These Threats?
Not all hosting companies offer the same level of protection (which is why you need platform like HostScore.net). Here’s how to evaluate your host’s security features before your site becomes a target.
- Does the host include malware scanning and removal? Some hosts offer built-in malware detection that scans your site daily. Look for plans that include automatic malware removal or alerts. For example, HostArmada includes free malware scans on all shared and WordPress plans.
- Are Web Application Firewalls (WAF) or server firewalls in place? A WAF helps filter out malicious traffic like XSS, SQL injection, and brute-force login attempts. Some managed hosting services, including Kinsta and WP Engine include WAFs by default, while others require manual setup through tools like Cloudflare or Imunify360.
- How isolated are sites on shared servers? If you’re on shared hosting, make sure the provider supports account-level isolation. This prevents malware from spreading between accounts.
- Is there DDoS protection? Check whether the host includes DDoS mitigation tools or integrates with providers like Cloudflare. For example, Namecheap includes basic DDoS protection on most plans, but LiquidWeb partners with Cloudflare Enterprise for higher-tier mitigation. Read this guide to find recommended web host with built-in DDoS protection.
- Does the provider support automatic software updates? Outdated WordPress cores, plugins, or server software are easy entry points for attackers. Managed WordPress hosts like Rocket.net and WP Engine automatically update WordPress and plugins, reducing your risk of running vulnerable versions.
- Are SSL certificates included and easy to install? A valid SSL certificate encrypts and protects data between your site and visitors. Many hosting companies now offer free Let’s Encrypt SSL with auto-renewal. If your host charges extra for SSL or makes setup difficult, consider switching.
- Does the host use strong cryptographic standards? Ask if your host enforces modern TLS versions (1.2 or 1.3), disables weak ciphers, and supports HTTP/2. This reduces the risk of cryptographic downgrade attacks or insecure handshakes.
Final Thoughts
When the majority of us think about website security, it is usually from the angle of overcoming the weaknesses of our own websites. However, as this article highlights, your hosting provider plays a critical role in protecting your site from broader infrastructure-level threats.
A secure host doesn’t just store your website — it also isolates accounts, filters attacks, and patches vulnerabilities before they reach your files. That makes hosting security just as important as application security.
You can’t force a host to improve its defenses, but you can choose one that prioritizes server security. Look for providers that offer malware scanning, firewalls, isolated environments, and automatic updates. These are signs that they take protection seriously for both their servers and your site.
Avoid hosting companies that treat security as an afterthought. The real value of web hosting goes beyond storage and speed; it includes trust, uptime, and peace of mind.









