Firewalls and Web Application Firewalls (WAFs) are core components of hosting security. While both tools help defend against cyber threats, they operate at different layers of the network and serve distinct purposes.
A firewall protects servers and networks by filtering traffic based on rules related to IP addresses, ports, and protocols. It helps prevent unauthorized access, lateral movement, and brute-force attacks.
A WAF, on the other hand, secures web applications. It inspects HTTP requests and blocks threats like SQL injection, cross-site scripting (XSS), and abuse of vulnerable endpoints.
But how do these tools work in web hosting; and which one matters more when choosing a hosting provider?
What Does a Firewall Do?
A firewall is a security system that filters inbound and outbound traffic based on pre-defined rules. It acts as a gatekeeper – allowing or blocking traffic depending on criteria such as IP address, port, protocol, or geographic source.
Firewalls operate at the network and transport layers (Layers 3 and 4 of the OSI model), making them well-suited for:
- Blocking untrusted IP ranges
- Throttling suspicious port activity
- Preventing external access to internal server resources
What Are the Types of Firewalls?
There are three common types of firewalls:
- Network firewalls: Protect entire server networks by inspecting all traffic between internal systems and the outside internet.
- Host-based firewalls: Installed on individual servers or VMs to manage device-level security policies.
- Cloud firewalls: Deployed through hosting providers or cloud platforms to secure infrastructure at scale.
Web hosting companies often include perimeter or cloud-based firewalls as part of their default security stack. These firewalls help shield hosting environments from DDoS attacks, port scanning, unauthorized logins, and malware propagation.
Vendors like Sophos, Cisco, and Palo Alto offer standalone firewall solutions, while bundled antivirus suites (e.g., Norton, McAfee) often include basic firewall capabilities for consumer endpoints.
What Does a Web Application Firewall (WAF) Do?
A Web Application Firewall (WAF) filters and monitors HTTP and HTTPS traffic between the web and your application. Unlike traditional firewalls that focus on low-level packet inspection, WAFs operate at the application layer (Layer 7), where user input, API calls, and dynamic content reside.
WAFs specialize in blocking:
- SQL injection attacks
- Cross-site scripting (XSS)
- Remote file inclusion
- Malicious bots and spam requests
By analyzing request patterns and payload content, WAFs can prevent unauthorized actions—such as admin panel access or data exfiltration—before they reach your web server.
WAFs can be cloud-based (e.g., Cloudflare, Sucuri, AWS WAF) or integrated into the hosting stack using server modules like ModSecurity.
What Are the Key Functions of a WAF?
- Inspects application-level traffic to detect known and zero-day attack patterns
- Blocks malicious payloads using signature- and behavior-based filtering
- Prevents data leaks by enforcing input validation and access rules
- Mitigates DDoS at the application level, protecting against slow POST, comment spam, or forced login attempts
- Improves site security posture without requiring changes to application code
Whether you’re on shared, VPS, or dedicated hosting, choosing a provider that includes a managed or integrated WAF adds a critical layer of defense.
Top hosting providers often include WAFs by default to protect popular CMS platforms and automatically updated with the latest threat intelligence.
What’s the Difference Between a Firewall and a WAF?
While both firewalls and WAFs are designed to protect networks and applications from attacks, a WAF is specifically designed to protect web applications from web-based attacks, whereas a traditional firewall is designed to protect the network as a whole.
WAFs offer a higher level of protection against web-based threats as they are able to inspect and filter web application traffic at the application layer. However, they cannot replace the need for a traditional firewall as firewalls offer protection at other network layers and can block other types of threats that a WAF may not detect.
| Security Feature | Firewall | WAF |
|---|---|---|
| Primary Protection Against | Network-based threats | Web-based attacks |
| Best For | Servers, databases, internal systems | Websites, web applications, APIs |
| Blocks | Unauthorized network access | SQL injections, XSS, and bot attacks |
| Layer of Protection | Network Layer | Application Layer |
| Use Case | Securing hosting servers, preventing unauthorized access | Protecting websites from hacking attempts |
How Do Web Hosts Use Firewalls and WAFs?
Does Your Hosting Provider Include a Firewall?
Most web hosting providers include some form of firewall at the infrastructure level, typically a network-level or perimeter firewall that filters malicious traffic before it reaches the server.
On shared hosting, this firewall is managed entirely by the provider and protects all accounts on the same server. On VPS or dedicated hosting, users may be responsible for configuring their own firewalls using tools like iptables, UFW, or third-party solutions.

Some premium hosts also implement intrusion prevention systems (IPS) and geo-blocking rules as part of their firewall strategy. These firewalls block common port scans, brute-force login attempts, and distributed denial-of-service (DDoS) attacks at the network level.
If your provider doesn’t mention firewall coverage in its plan specs or support documents, it’s worth asking whether one is included and what level of protection it offers.
How WAFs Protect Websites in Shared and Cloud Hosting?
A Web Application Firewall (WAF) filters traffic at the application layer – monitoring HTTP requests and blocking threats like SQL injection, cross-site scripting (XSS), and other OWASP Top 10 vulnerabilities.
On shared hosting, WAFs are usually applied globally by the provider. These are managed and updated centrally, meaning users don’t need to configure individual rule sets. Popular setups may use tools like ModSecurity with custom rule packs tailored to common CMS platforms like WordPress or Joomla.

In cloud hosting environments, WAFs are often integrated with reverse proxies or edge services like Cloudflare, Sucuri, or AWS WAF. These setups offer more flexibility, such as IP whitelisting, bot detection, and rate limiting.
The benefit of having a WAF in shared or cloud hosting is that it provides strong security coverage without requiring technical configuration. However, the quality and responsiveness of the WAF depend entirely on the provider’s infrastructure.
Are WAFs Standard on Managed WordPress Hosting?
Yes, most managed WordPress hosting providers include a WAF as part of their default security stack. These WAFs are tuned specifically for WordPress and help defend against:
- XML-RPC and REST API abuse
- Unauthorized login attempts
- Plugin or theme vulnerabilities
- Malicious file uploads
Web hosts like Kinsta and WP Engine use server-level WAFs combined with malware scanning and traffic filtering. Some also include integration with third-party security providers like Cloudflare Enterprise or Imunify360.
A WAF on managed WordPress hosting ensures that security is handled automatically, even for non-technical users. This is especially useful for site owners running eCommerce stores, membership platforms, or community forums where user input is frequent and complex.
How Do Firewalls and WAFs Affect Website Performance?
Firewalls and WAFs can affect website performance, both positively and negatively, depending on how they’re implemented.
Properly configured, they can improve performance by filtering out malicious bots, reducing spam traffic, and preventing resource overuse. But if misconfigured or overloaded, they can introduce latency or interfere with caching mechanisms.
Let’s look at two key areas of concern:
CDN and WAF Compatibility
When using a CDN alongside a WAF, compatibility becomes essential. Some WAFs function as part of the CDN layer (e.g., Cloudflare), while others are hosted on the origin server.
If both the CDN and the WAF try to modify or inspect the same request headers, you may encounter SSL handshake issues, redirect loops, or CAPTCHA conflicts. Ensuring that your CDN and WAF are properly integrated is key to preventing these issues.
Web hosts that offer pre-integrated CDN + WAF stacks generally avoid these pitfalls by handling configuration internally.
Latency and Caching Considerations
Firewalls and WAFs can introduce additional processing time, especially if they inspect every incoming request in real time. This can affect Time to First Byte (TTFB), particularly on high-traffic sites or when using complex WAF rulesets.
Caching can mitigate some of this impact. However, poorly configured WAFs may interfere with full-page caching or prevent dynamic content from being served efficiently.
Look for providers that offer optimized WAF setups with smart caching integration—or allow you to whitelist safe requests and paths to improve load times.
What Happens If Your Web Host Lacks Firewall & WAF Protection?
Without a firewall and Web Application Firewall (WAF), websites and hosting infrastructure are vulnerable to cyber threats that can result in data breaches, downtime, and financial loss.
For businesses, this is especially critical – compromised customer databases, leaked employee records, or unauthorized access to sensitive hosting environments can lead to reputational damage and regulatory penalties.
Risks of Not Using a Firewall
Neglecting to implement a network firewall exposes your hosting server to:
- Privilege escalation: Attackers who gain initial access can exploit vulnerabilities to increase their control and access other areas of the system.
- Unauthorized access: Weak authentication or compromised credentials can allow hackers to infiltrate hosting servers and databases.
- Man-in-the-Middle (MITM) attacks: Cybercriminals can intercept network traffic, capturing sensitive data such as login credentials and payment information.
Risks of Not Using a WAF
Web applications are a primary target for cybercriminals, and failing to use a WAF leaves websites exposed to application-layer threats, including:
- SQL injection (SQLi): Attackers can inject malicious database queries, leading to stolen customer data, defaced websites, or deleted records.
- Cross-site scripting (XSS): Malicious scripts can be inserted into website code, allowing hackers to steal session cookies or spread malware to visitors.
- Denial-of-Service (DoS) attacks: Attackers can overload web servers with excessive requests, crashing the website and disrupting online business operations.
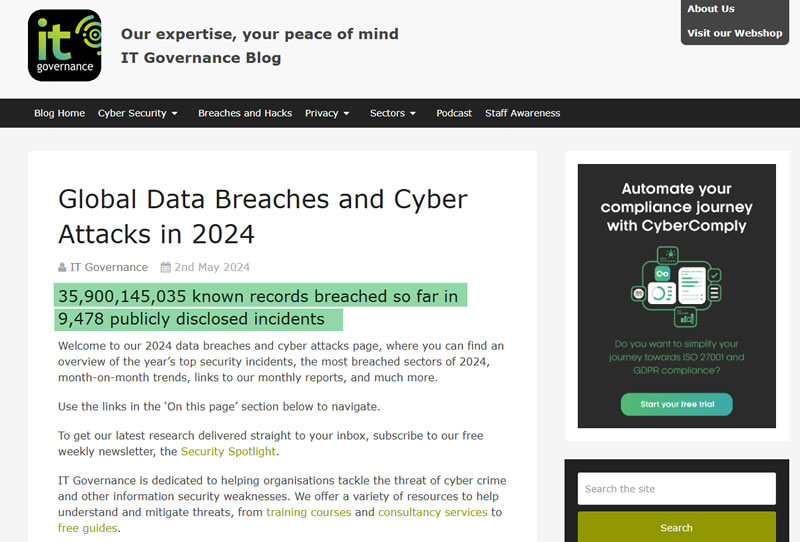
Real-World Examples of Sites Compromised Without These Tools

Firewall and WAF protection are fundamental layers in any hosting security stack. When these tools are missing or misconfigured, even well-funded organizations can fall victim to attacks. Here are real-world examples that show the consequences:
1. Fortune 1000 Companies Exposed via “BreakingWAF” Misconfigurations
In late 2024, Zafran Researchers discovered a widespread vulnerability dubbed “BreakingWAF” that allowed attackers to bypass improperly configured WAFs deployed by top CDN and security providers including Akamai, Cloudflare, Fastly, and Imperva. The flaw exposed over 140,000 domains, including those owned by JPMorgan Chase, Intel, Visa, Berkshire Hathaway, and UnitedHealth.
Affected sites became vulnerable to DDoS attacks, ransomware delivery, and full server takeovers. Many organizations believed they were protected, but their WAF policies were too broad or lacked strict rule enforcement.
2. Capital One Breach: Misconfigured WAF and SSRF Exploitation
In 2019, Capital One suffered a breach that exposed the personal data of over 100 million customers. The root cause was a Server-Side Request Forgery (SSRF) vulnerability, which the attacker exploited via a misconfigured open-source WAF (ModSecurity) deployed in Capital One’s AWS environment.
The WAF failed to block malicious requests, allowing the attacker to access internal metadata services, extract AWS credentials, and ultimately download sensitive files from Amazon S3 buckets.
3. DDoS and Ransomware Risks from WAF Misconfigurations in the Fortune 1000
The BreakingWAF research also revealed that more than 8,000 misconfigured domains, spanning 135 Fortune 1000 companies, exposed over 36,000 backend services to the public internet. These included open RDP ports, vulnerable admin panels, and legacy APIs with no authentication.
Without proper WAF protections or access restrictions, these endpoints became easy entry points for ransomware and denial-of-service attacks.
Key Takeaways
Firewalls and WAFs are complementary tools – not competitors.
A business using a hosting provider to run web applications, eCommerce platforms, or membership sites needs both a firewall for infrastructure security and a WAF for application-layer protection.
For individual website owners, a WAF is usually included in managed hosting plans to block common web threats, while a traditional firewall is more relevant for server administrators managing VPS or dedicated hosting.
Whether you’re selecting shared hosting, VPS, or dedicated hosting – prioritize a provider with strong security measures. Look for firewall and WAF integration, along with DDoS protection, malware scanning, and automated security updates. Before committing, take advantage of free trials to ensure your hosting provider meets your website protection needs.



